Secure Email Setup for Mail 10 & OS 10.12 Sierra
Sierra: As good as Mavericks, if you redo your certificate!
Security indicators are finally back, for the first time since Mail 7 and OS 10.9 Mavericks! Sadly, the other bugs remain, and that’s why this article exists. The Sierra experience looks and works like OS X 10.10 Yosemite and 10.11 El Capitan. Even though the major version numbers of Keychain Access and Certificate Assistant are identical to Mavericks 10.9, the build numbers are different.
The other big news with the Sierra bundle is that for the first time, Apple requires the Key Usage Extension (KUE) to exist and be properly filled out for there to be any hope of S/MIME to work in Mail. If your existing certificates have the KUE, you’re good to go. If you’ve followed the instructions on this series of articles in the past recommending omitting the KUE, you’re hosed: you need to make new self-signed certificates with a proper KUE.
The following instructions have been formulated running macOS 10.12.6, its Mail 10.3, Safari 10.1.2, Keychain Access 9.0 (55208.60.1), Certificate Assistant 5.0 (55165.50.2), and all current updates to these items as of 27 August 2017. They will likely work the same with earlier versions of OS 10.12 and its components, but i never tested those earlier versions. These instructions will probably continue to apply to any later updates as well, though versions newer than those listed above have not been explicitly tested by me.
These instructions assume you already have at least one working email account set up and properly operating in Mail (in the usual insecure manner of standard Internet email). If you don’t, please go set it up and test it now, following Apple’s/other’s instructions.
Creating a Self-Signed S/MIME Certificate-key pair
- Quit Mail, if it is running.
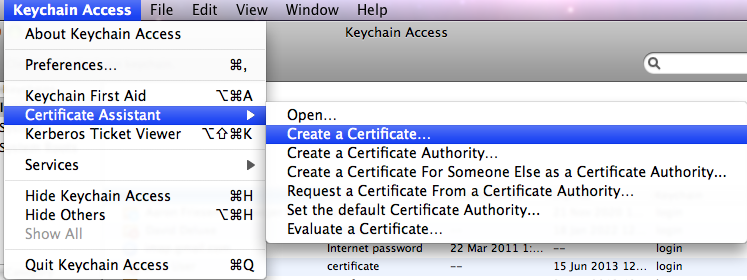
- Open Keychain Access (from the Utilities folder). From its eponymous menu, select and :
- Certificate Assistant version 5.0 will run. You’ll be presented with the window:
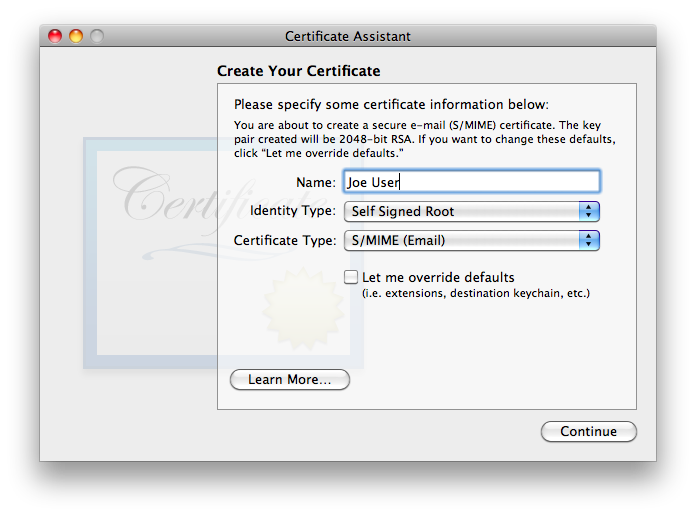
is exactly the type of certificate we wish to create. Given that S/MIME (Email) is most definitely the Certificate Type we want, one might think that it would be OK to merely verify the name and click . But Apple chose inappropriate default settings, so default certificates can never work correctly!—even still with the Sierra-bundled software. The biggest problem is that Certificate Assistant never asks for/confirms the email address, without which the certificate is useless for email! In many (but not all) cases, Certificate Assistant fails to insert any email address whatsoever into a default certificate, rendering it useless for email. Even in cases where Certificate Assistant finds one or more email addresses, when there is more than one, Certificate Assistant does not allow the user to select which one to use. Equally severe, Apple neglected to default select Key Encipherment for the Key Usage Extension, so even if the email address is present and correct in the default certificate, it cannot be used for encrypting outgoing messages… only for signing them. As of this writing, Apple has not fixed this problem, all the way through the most recent version tested, OS 10.12 Sierra. Note that even though OS X versions 10.6 through 10.11 contain an added layer of complexity to work around these mistakes, this added layer is not backward-compatible with older OS X versions, nor in my testing with Sierra and its Mail itself! It is also unlikely to be compatible with non-Apple systems.Even if Apple hadn’t made the several errors which render a default certificate useless for secure email, the default lifetime for the certificate is set for one year. Most people will find renewing their certificate each year—and getting all their correspondents to renew it as well!—a huge hassle not worth undertaking. For all these reasons, be sure to check .
- Click , and you’ll see:
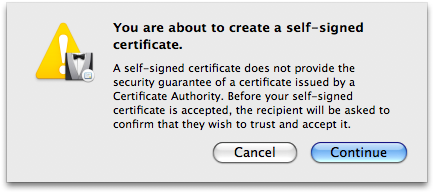
If, after reading Apple’s warning, any of you are not comfortable at this point and want to go to the trouble of paying a reliable Certificate Authority (CA) for a guaranteed certificate and following their instructions for installation, or wish to hunt around for any CAs who may be still offering free certificates for personal use (and jump through their hoops), by all means go ahead… see ya ’round! The rest of us will simply click and move on. - Because of the necessity of overriding the defaults, you’ll now be presented with a series of detailed settings windows. The first of the series of detail windows——asks you to fill in basic information:
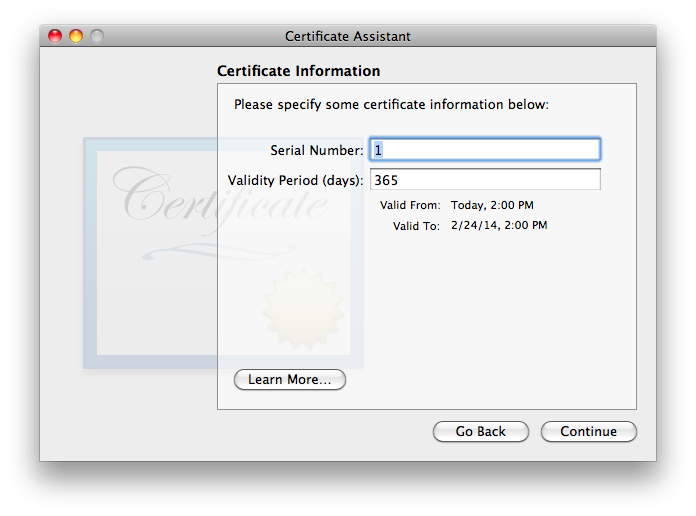
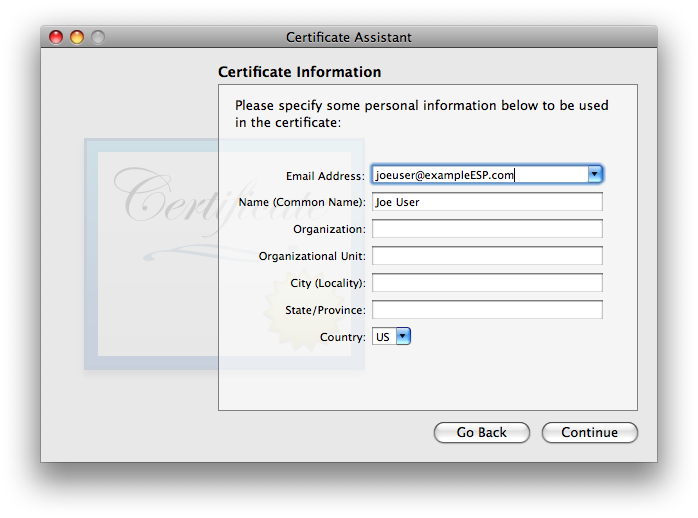
I have not found that the Serial Number matters, in my testing. If you think you may wind up having multiple certificates for the same user name and/or email address on one system, it is probably a good idea to ensure that the serial numbers differ (though i did not find any issues in brief testing where they were the same). I strongly recommend choosing a longer Validity Period, to minimize the hassle of re-creating a new certificate, distributing it to all your secure correspondents, and getting them to do the work to get the new one trusted on their system(s). The tradeoff with a longer time is that there is a much longer time span over which the valid certificate may be compromised by some malefactor getting ahold of your security credential set (certificate + public & private keys) and pretending to be you. I’m finding that 10 years is working as a decent compromise, so i usually fill in the box with 3652 (approximately 10 years, measured in days). Once these items are verified/set, go ahead and click . - The second Certificate Information window asks for “personal information […] to be used in the certificate”. As discussed in the Points common to all OS versions section, the only essential item is the email address. Entering a Common Name is highly recommended, as it will make it easier to find the certificate in keychains, on backups, etc. The other items are optional. They may be filled out frivolously, though if the certificate might ever be used for other purposes or on non-Apple systems, there might be cases of failure if certain fields do not match reality (or at least expectations). Note that all this information becomes part of the certificate you’ll be sharing with the outer world.
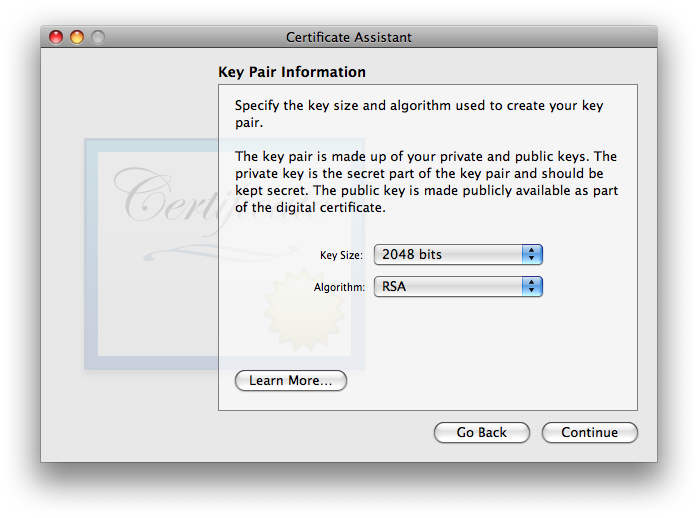
click when finished. - You will now be asked to approve . The defaults of 2048 bits key size and RSA algorithm are good (to the point that i did not bother testing any other options. The newer ECC option looks intriguing, but it would not be backwards-compatible with Leopard 10.5 nor Tiger 10.4 systems, and possibly not with non-Apple systems, therefore i cannot recommend it). These values are generally regarded as secure (as of the creation date of this article). 2048 bits is the largest (most secure) option for RSA on all versions of OS X from Tiger through Sierra (and hopefully will remain compatible with newer macOS/Mail versions released in the future). I also notice that with Certificate Assistant 5.0 on El Capitan and Sierra, 2048 bits is the only allowable key size option.
Click . - Next you’ll be offered the settings. Details for this extension are discussed on the separate page X.509 v3 Certificate Extensions. Here again, Apple made a mistake: the certificate cannot work for encrypting outgoing email messages unless Key Encipherment is selected!
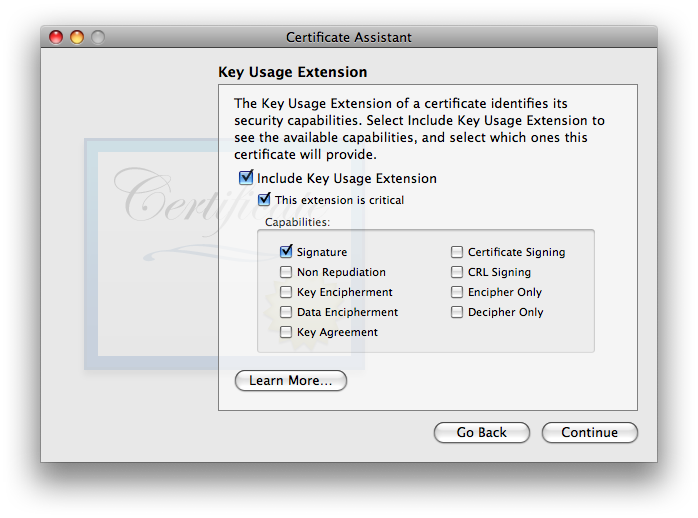
I used to recommend disabling (unchecking) “Include Key Usage Extension”, however due to changes made by Apple as of 10.12 Sierra, the Key Usage Extension MUST be included for a certificate to be valid. If you wish for your certificate to work on Sierra or newer as well as all OS X/Mail versions back to 10.4 Tiger/Mail 2, you must enable Key Encipherment (and leave Signature enabled). Once you’ve made your selection(s), click . - Next you’ll be hit with the settings:
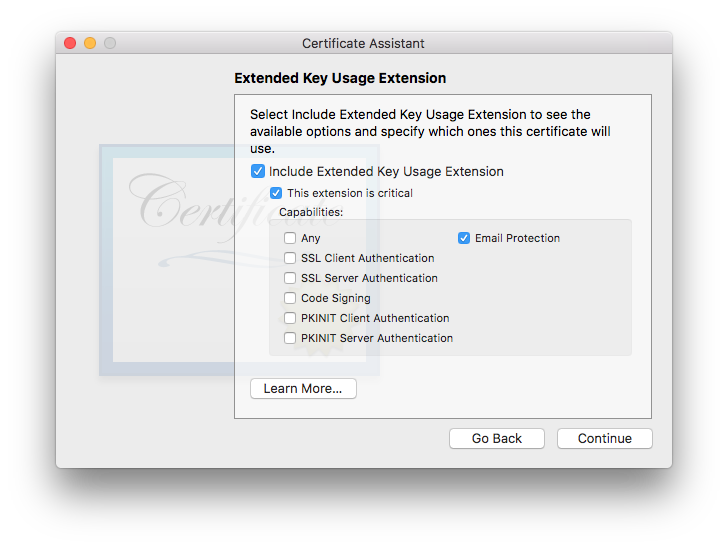
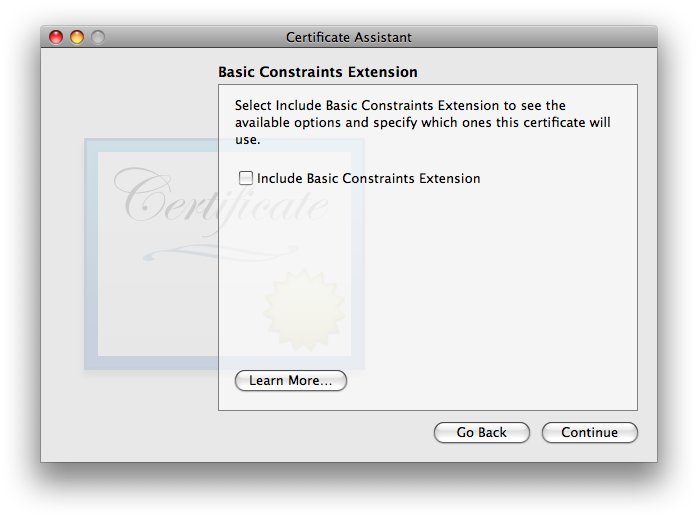
This one’s defaults are OK. It is OK to include it if you want, or disable it if you want—both ways work, in my testing. I tend to leave it engaged with settings as shown, in case future software starts to get picky about seeing specific usages indicated within certificates. As always, click to move on. - The gets us back into a controversial area where the experts are not in agreement. Some say that this extension should always be enabled and “Use this certificate as a certificate authority” (which will appear in this window when Basic Constraints is enabled) should be checked, for all self-signed certificates. Others disagree. In my testing, i left it at its default—disabled—and things worked fine.
- The last of the array of extra-work-making extensions is the (which i’ll abbreviate: SANE):
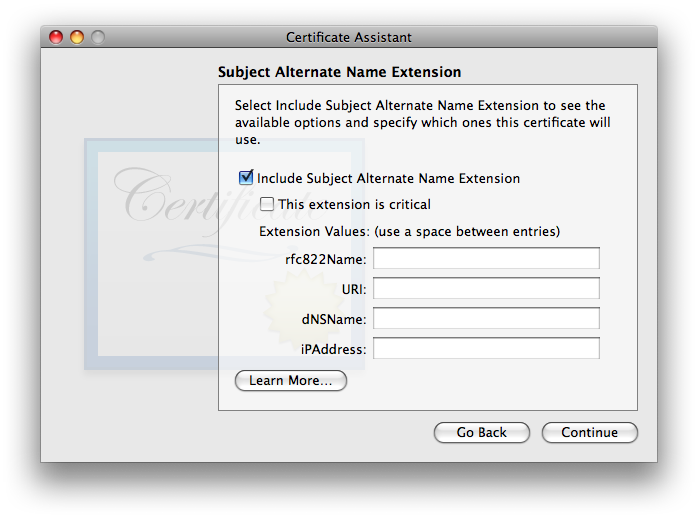
As discussed in the SANE section of the X.509 v3 Certificate Extensions page, SANE is not required. I did a lot of testing with and without it, with no difference in results. If it is used, it is essential that the rfc822Name field include the same exact email address as listed above under Certificate Information. Normally, Certificate Assistant fills this in automatically and correctly, so all you’ll need to do is double-check it. If for some reason it shows up empty as in the screenshot above, carefully type it in, correctly: just the you@youresp.com part… nothing else. Once you’ve made your choices, click . - Finally, Certificate Assistant will ask you to :
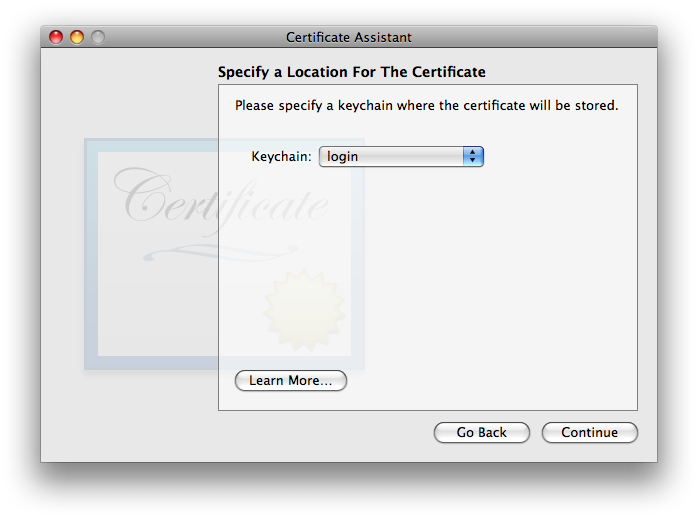
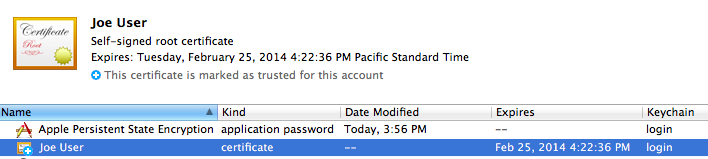
The default location of the login keychain is the correct answer. When you click , Certificate Assistant will now (finally) create the usual three items in your login keychain: the certificate, your public key, and your private key. See New Security Credentials part of the Points common to all OS versions section of the main article for further information.
Trusting a Certificate
Your public and private keys need no further attention—they’re ready to run. All they need to do is sit there on your system and work.
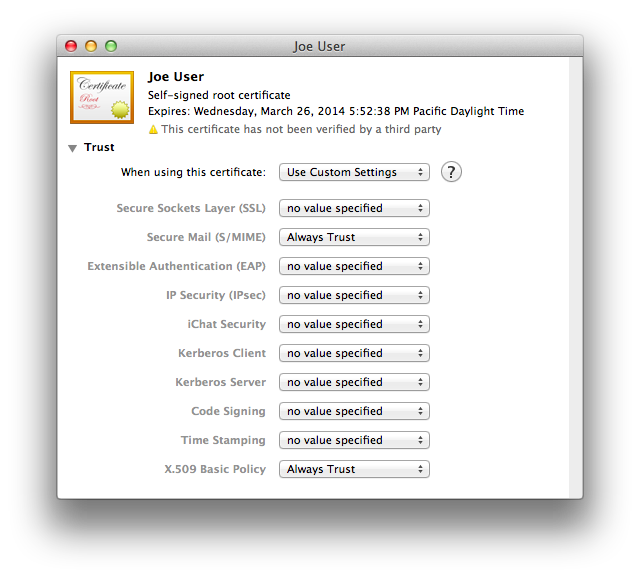
In Keychain Access, looking at your login keychain, double-click your newly-made certificate. You can select the category in the lower left column to filter out items in the main window frame which are not certificates, to make it easier to find. Click the arrow next to the word Trust just below the certificate icon, and the trust options will be revealed. Here’s what they’ll look like at first:
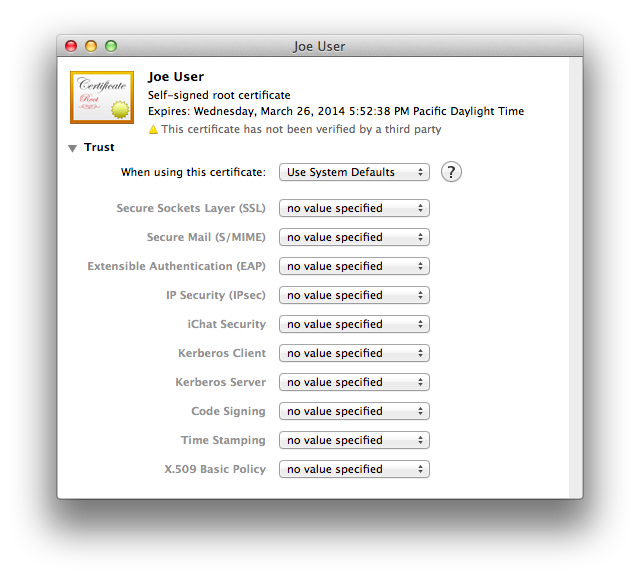
- Secure Mail (S/MIME)
- X.509 Basic Policy
Preserve Your New Security Credentials: Back Up!
Now is the time to back up your new certificate, public key, and private key, archive them, or both!
Please see Backing up your new security credentials on the common page for all the step-by-step details.
Other Machines?
As discussed in the Sharing One Set of Credentials with Other Machines part of the Points common to all OS versions section of the main article page, one set of email security credentials should be used on all devices you own.
The easiest and possibly best way to do this is to place a copy of the keychain you made with your 3 security credentials on each device and import the items from there. Here’s how it works moving these credentials to a different Mac:
- Place a copy of your secure email credentials keychain on the Mac. I tend to put it on the desktop.
- Double-click the credentials keychain file. Keychain Access should open, and the keychain should be visible in the list, shown locked.
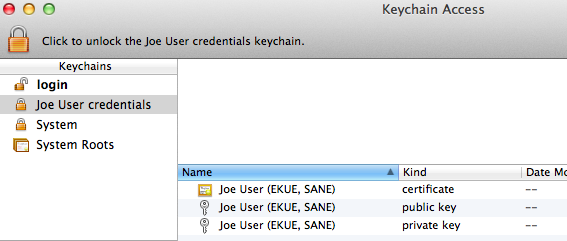
- Select the credentials keychain. Select two of the 3 items: certificate and private key, within the keychain and drag them to the login keychain. The public key is contained in the certificate, and in my testing you’ll get an obscure error message if you attempt to bring it along as well. It is useful to have in your credential archive in case you move to a PGP variant or somesuch which uses public keys instead of certificates with embedded public keys.
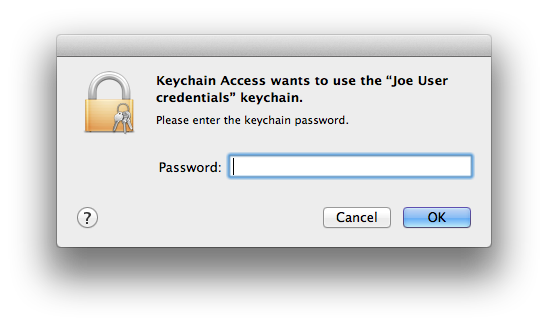
- Keychain Access will now ask for the password/passphrase for the credentials keychain. Enter it.
- The certificate and private key will move out of the importing keychain into the login keychain.
- The certificate is not ready for email yet. Double-click it in the login keychain. Be sure both and are set to . Close the window.
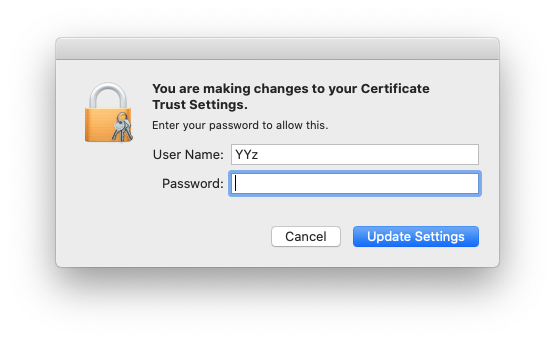
- You will see the change to certificate trust settings window. OK the change of certificate trust settings with your current OS X user credentials.
- Delete the credentials keychain (now with just the public key) from within Keychain Access via the option in the menu.
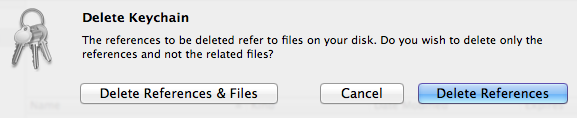
Select to get rid of both the references inside the Keychain Access application itself and the actual credentials file, now nearly empty (you did use a copy of this file in the first step of this sequence, didn’t you?). The deleted keychain might vanish immediately or remain in the list of keychains until Keychain Access is quit and reopened (no need to do that now), depending on things like permissions. - Quit Keychain Access. Done!
If instead of saving the 3 credential items in a separate keychain you exported each item individually, you will need to use in Keychain Access on each of your backed up/archived .cer and .p12 files for the certificate and private key, respectively. Don’t bother exporting the public key (.pem) for S/MIME usage, as it’s more work, is not needed, and you’ll only get an error message.
Due to bugs in Keychain Assistant (and/or the security infrastructure) for OS X all the way from Tiger through Lion (at which point i ceased testing this individual item method), then again when i tested Sierra, during my testing the certificate went in to the new system just fine, but there was an error message for both the public and private keys (i only tested the private key on Sierra, and the wording may not be identical, but is close):
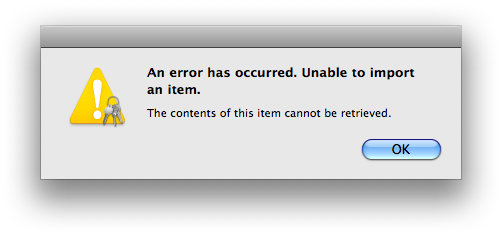
The private key went in despite this error message; the public key did not. This problem occurs whether i double-click the file in Finder or use within Keychain Access. Thankfully the public key truly is redundant, and the private key does import despite the error message!
Verify that Setup is Complete
This completes the setup for your email security credentials at your end. Quit Keychain Access. Launch Mail, and open a new message form. If all is well, you should see a new pair of icons in the lower right part of the header area, just above the white message body area:
![]()
Yours may or may not look like the screenshot: your seal may have an x in it instead of a checkmark. If you have more than one email account and the currently-selected account in Mail is not the one for which you just created security credentials, both icons may be grayed out. As long as you see these two icons in some form (gray, black, or blue, selected or not selected), you have successfully completed setup. The final step is to exchange certificates with your correspondents.
Trusting Others’ Certificates
When you first receive an email message with a new, self-signed certificate, Mail will not be able to trust the certificate and will alert you to this fact, first with a banner:
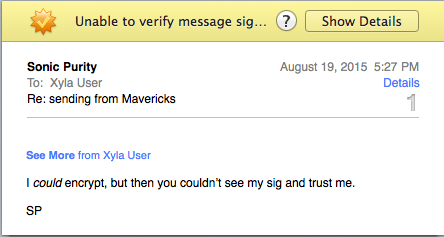
Due to at least one straggling bug amazingly still in place in OS 10.12 Sierra which was one of many also in OS 10.7 Lion through 10.11 El Capitan, do Not do Not do Not go through the process of showing details and eventually trusting the certificate from within Mail—it’s broken and it doesn’t work! It looks like it works and it might possibly intermittently work for some people some of the time, depending whether Keychain Access is running or quit and likely due to other factors beyond what i can track. It can and will show the message as signed, but if you try to send an encrypted reply, no encryption for you-oooh! See “Can’t Encrypt a reply email immediately after trusting an incoming certificate”, immediately below this section. (If you want to see what it would look like if it did work, go to this section on the page in this series of articles for OS 10.6 Snow Leopard.)
Quit Mail and follow the same instructions above to use Keychain Access to trust the certificate, as you did previously for your own.
Bugs and Problems
Security credentials which worked perfectly between OS 10.4 Tiger and OS 10.11 El Capitan no longer work!
As of macOS 10.12 Sierra, Apple changed the security requirements Mail 10 and later consider acceptable for a properly formed S/MIME certificate. On the older OSes and versions of Mail, it did not matter whether the Key Usage Extension (KUE) was present or not. Now it matters. Unfortunately if your existing certificate lacks a properly filled out KUE (signature and key encipherment checked), it cannot be made to work with Mail 10 in OS 10.12 (and likely later). You will need to create/obtain a new certificate with a proper KUE. I have updated the older OS/Mail pages as well as providing the currently-correct KUE information on this page, to help with the process. The good news is that your new cert will not only work on Sierra (and probably newer), but will work all the way back to Tiger 10.4.11/Mail 2.1.3, like your old KUE-less one used to.
As of the moment, the Extended Key Usage Extension (EKUE) remains optional, as does the Subject Alternate Name Extension (SANE). It may not hurt to leave them at the Certificate Assistant defaults, which don’t harm anything and look legit moving forward to the future, in case either or both become requirements later on.
Can’t Encrypt a reply email immediately after trusting an incoming certificate
Padlock remains grayed out, even though the certificate shows as trusted. This currently happens if you try to allow Mail to change the trust settings of a certificate.
Workaround: If you find yourself stuck in this situation:
- Quit Mail, if it is running.
- Open Keychain Access. Double-click the troublesome certificate (the one you received from someone else and mistakenly tried to trust within Mail).
- Change “When using this certificate” to “Use System Defaults”. Close the certificate window to save the changes (very important), authenticating as needed.
- Re-open (double-click) the certificate and its trust settings area. Change both and to . Close the certificate window (again) to save the changes.
Anyone at Apple wanting to look into this should check my Radar bug, #11742852. This bug was reported 25 June 2012 and as of 27 August 2017 is still not fixed, making me wonder whether 20-teens Apple ever fixes its bugs (wrote the former 1990s Apple software QA tester). It would be really nice if Apple finally fixed this bug, before Apple abandons Sierra… El Capitan… Yosemite… Mavericks… (etc. sigh etc.). Feel encouraged to send Apple feedback if you’d like to see this bug fixed.
Can’t Encrypt an outgoing email message: Can’t Lock Padlock
Many things can cause this failure, esp. in Lion and all newer OS X and macOS versions, so far. Here are the ones i know:
- Do Not change Trust settings via Mail! See the item above.
- With Lion and all newer OS X/macOS versions through (so far) Sierra, one has to explicitly trust both the recipient’s and the sender’s security credentials in Keychain Access. Even though the message is being encrypted to the recipient using the recipient’s public key (in their certificate), i have seen a case where the sender’s Mail refused to allow the padlock to be locked until the sender’s certificate was fully and correctly trusted in Keychain Access.
- Verify that the recipient’s certificate allows for encryption. For Sierra and newer, the certificate must have the Key Usage Extension, and Key Encipherment must be selected. This is not the Apple default in any version of Certificate Assistant released through 27 August 2017.
Comments? Found an error? Let me know, and i’ll see what i can do.